Cloud repatriation: 5 reasons why enterprises are self-hosting their design tools
Why are design platforms overlooked in cloud repatriation plans? Discover 5 reasons enterprises self-host design tools for security, compliance, and cost control.

More and more companies are considering the benefits of cloud repatriation for their businesses. Recent data shows 67% have already repatriated some workloads, and 87% plan to move more in the next 12–24 months.
However, when teams move applications and data from public cloud back to on-premises data centers, private clouds, or hybrid setups they control directly, they focus on databases or analytics. Design platforms rarely make the list. Yet these tools hold some of your most sensitive assets, whether that’s product concepts, brand strategies, or workflow data.
For companies already involved in or just considering some form of cloud repatriation, it's important to remember that there are real benefits to doing the same thing for your design data. In this guide, we'll explain why design tools deserve the same infrastructure sovereignty as your code repositories, walk through five reasons enterprises are choosing to self-host, and show how open source platforms like Penpot make it practical to bring your design stack back under your control.
Why design tools are critical infrastructure that demands sovereignty
Design files contain competitive intelligence just like your source code and financial data, yet receive a fraction of the security and control protections. Overlooking this gap may be shortsighted.
Think of design files as the visual equivalent of your source code repository. They document strategic decisions before they become public. A leaked file can reveal your Q3 product launch six months early. If you're already investing heavily in non-disclosure agreements (NDAs) and legal protections for design work, your storage and treatment of the work should align with its sensitive nature.
The same logic applies to your security posture. If you take a "never trust, always verify" Zero Trust approach with self-hosted GitLab, air-gapped staging environments, or on-premises CI/CD pipelines, design tools should follow the same standard. Design files frequently flow in and out of development workflows anyway, and they deserve protection.
Design data isn't just color logo files or app mockups. Competitive IP includes everything from unreleased product prototypes to pricing page experiments and customer persona boards. If you wouldn't feel comfortable sharing your UX research artifacts in a vendor's cloud, you may want to rethink storing any design files there.
Beyond security best practices, legal and regulatory requirements may push you toward stricter control of where design‑related data lives. User research, customer journey maps, and demographic data often fall under EU data protection laws such as GDPR when they can identify an individual directly (names, emails, IDs) or indirectly (unique IDs, detailed behavior logs, combined demographic traits). If you store personal customer data where you design, moving to your own servers could help you ensure compliance.
5 reasons enterprises are self-hosting their design tools
While design platforms are rarely the first workloads leaders consider when moving away from the cloud (most start with storage, analytics, or core apps), they’re increasingly part of repatriation plans as enterprises wake up to the cost, compliance, and vendor‑lock‑in risks tied to design data.
1. Cost predictability and eliminating per-seat pricing fatigue
While there’s always some cost for using a design tool, self-hosting contains some of the volatility by shifting spend to infrastructure you manage. It’s not uncommon to see proprietary design platforms increase prices by 20-33% in a single year (like Figma did in 2025). For a large design team, that amounts to thousands more paid annually with little warning or ability to negotiate.
Vendor-controlled pricing creates other predictability problems, too. Many platforms bundle features you don't need or use, forcing you to pay for the entire package to access basic functionality. Others layer on charges for integrations, API calls, or premium security features that should be standard. When costs are tied to vendor decisions rather than your actual usage or needs, budgeting becomes guesswork.
Self-hosting design tools, on the other hand, follow the same total cost of ownership calculation as self-hosting databases or CI/CD systems. You trade unpredictable vendor pricing for infrastructure on your own terms. You can scale hardware, optimize storage, or renegotiate hosting, giving finance and platform teams a clearer long-term view of design tooling costs. For stable, predictable workloads, on-premises consistently wins long-term.
2. Data ownership and IP protection
Vendor terms of service often grant themselves broad access rights for "service improvement" and "debugging." So, who truly owns your design files when they live in a vendor's proprietary cloud? While you may think your designs are yours, with others having access, it’s never a guarantee. If the vendor enters an M&A situation, you may experience legal challenges around who controls your IP, how quickly you can retrieve it, and whether the acquiring company can reuse or analyze your data under the old contract. Also, common operational headaches may include rushed migrations, rewritten DPAs, and new security reviews under an unfamiliar vendor stack.
Self‑hosting greatly reduces these risks because your files remain on infrastructure you control, even if the vendor’s ownership or business model changes.
For enterprises operating under strict data residency and sovereignty rules, this becomes more than a theoretical concern. Regulations such as GDPR, HIPAA, and industry‑specific frameworks increasingly treat design artifacts that reference users, markets, or internal strategy as regulated data, which means you must understand exactly where those files live and who can see them.
3. Security and compliance for regulated industries
For businesses in e-commerce, insurance, banking, or healthcare, there’s added pressure to comply with industry-specific regulations. Using a cloud design tool doesn’t transfer your compliance obligations; under shared responsibility models and laws like GDPR and HIPAA, you remain accountable for how data is stored and accessed, while providers have their own parallel obligations and potential liability.
We’ve already touched on how modern security frameworks for these sensitive industries require "never trust, always verify" at every layer. But most design tools sit outside the Zero Trust perimeter. They become the weakest link in your security architecture.
In practice, this becomes especially painful with design tools that depend on constant outbound connections to a vendor’s cloud. Every external integration, webhook, or background sync has to be documented, justified, and retested during security audits. Each activity increases the attack surface and slows compliance reviews. A tool that cannot function without external connectivity is very hard to fit cleanly into a Zero Trust model.
For air-gapped environments, such as defense contractors and classified government operators, cloud-based tools just won’t work. Currently, self-hosted tools are the only ways to meet requirements while enabling Unified Security Posture Management (USPM) for single identity, access, and audit logs across your entire organization. Since these workflows should also include design processes, it’s important to have a self-hosted option that fits.
4. Avoiding vendor lock-in and bait-and-switch pricing
Self-hosting creates freedom from unexpected price hikes or using file types you can’t take with you wherever you work. We’ve seen cautionary tales of both, most recently with discontinued products that companies had their workflows built around. When teams are forced to migrate mid-project, they must retrain staff, revamp workflows, and rebuild component libraries — all due to a decision beyond their control.
With SaaS pricing lifecycles as they are, it’s common to pay much less for the first year or contract and then see increases for feature upgrades, enhanced customizations, and more storage volume. Self-hosting may not eliminate all of these cost increases, but it does ensure you can make the best budget decisions for your organization without the fear of losing all your work.
Also, cloud repatriation with open formats like SVG and CSS keeps you out of the proprietary format trap. You own your files, in the format you prefer, and within your own infrastructure. If the vendor ever decides to bundle services you don’t want or need, you can easily walk away with your assets intact.
5. DevOps and infrastructure alignment
When your code repositories, CI/CD pipelines, and staging environments are self-hosted, design tools should follow the same infrastructure philosophy, allowing you to maintain architectural consistency, regardless of vendor preference.
For example, many enterprises have an authentication fragmentation problem. Self-hosted DevOps tools typically integrate with enterprise LDAP, OIDC, or SAML SSO. But cloud design tools require separate authentication, which fragments your identity management and creates audit blind spots.
And many designers work in cloud-based tools, while developers work in self-hosted repositories. You’ve created an artificial barrier to collaboration, complete with different access controls, different versioning systems, and different security policies.
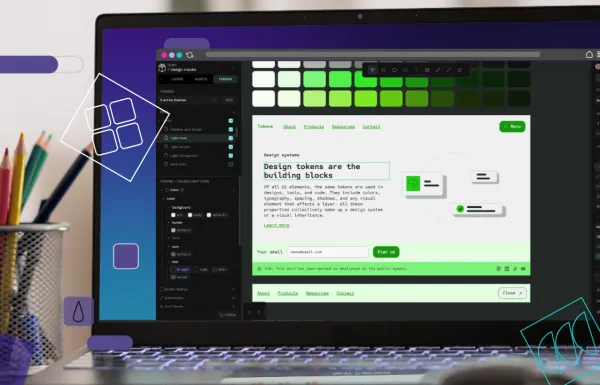
Penpot is designed to act as a single source of truth for your design system and to integrate closely with your code workflows. Because Penpot works with open web standards like SVG, CSS, HTML, and JSON, your design artifacts can be stored and versioned alongside code, documentation, and infrastructure‑as‑code configs in your existing repositories if you choose.
Penpot can also integrate with enterprise authentication systems like LDAP and OpenID Connect, so you can tie design access into the same identity provider as your DevOps stack and reduce identity fragmentation. For teams with stricter governance requirements, Penpot’s security and compliance approach adds another layer of confidence.
Plus, with native design tokens that follow the W3C DTCG draft standard, you can wire Penpot into your CI/CD or component pipelines so that design‑system changes drive automated updates to component libraries, with all resulting actions logged by your existing tooling.
This means that when you connect Penpot to your centralized logging and version control, design and code changes can be recorded in the same queryable audit trail, giving teams a far more unified view of the product development lifecycle.
Self-host your design workflow with Penpot
Design tools are a critical infrastructure that deserves the same sovereignty consideration as code repositories and databases. Cloud repatriation isn't a trend, and it will soon include strategic realignment around control, compliance, and cost predictability for all tools (even design platforms).
It’s true that self-hosting isn't for everyone, as it requires infrastructure expertise, DevOps resources, and a willingness to manage deployments. But for enterprises already self-hosting their dev stack, Penpot is a natural extension of existing capabilities.
The question isn't "Should we self-host design tools?" It's "Can we afford the vendor risk, compliance exposure, and cost unpredictability of not self-hosting?"
Talk to our team for more information about your enterprise deployment options.
Related blogs
Interested to learn more about how enterprises can benefit from self-hosting? Here are more articles: